Sales: +91 96000 06934
- Support
Every PAM tool works when your infrastructure is reachable. The real test is what happens when it isn't.
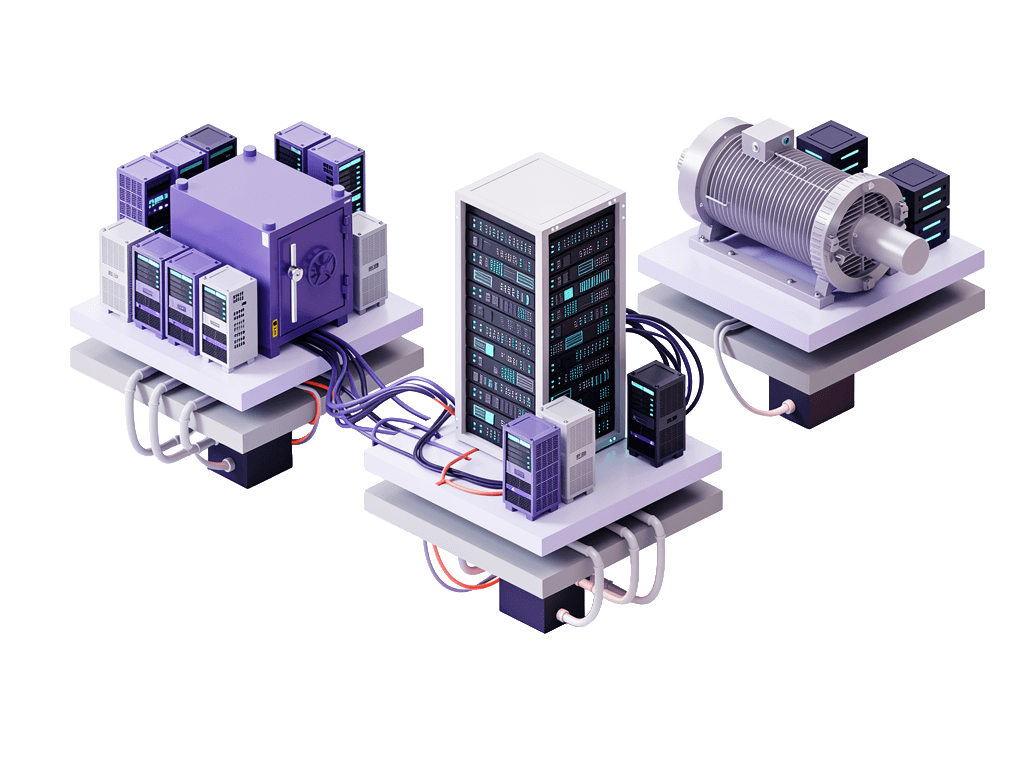
Isolated networks; on-premise datacenters with strict firewalls, private cloud VPCs, regulated industry environments where no inbound traffic is permitted, fully air-gapped systems; are where most PAM tools either break down entirely or require you to deploy their full product stack inside every zone you want to manage. Akku is built differently. AkkuArka and AkkuReka stay central. A lightweight Akku agent is deployed inside the isolated network. The agent makes only outbound connections. Your firewall never needs to accept a single inbound rule.

Built differently
Every architectural choice Akku makes is designed for the networks where conventional PAM tools fail.
One lightweight agent binary per isolated network — no full product stack inside the zone.
The agent makes only outbound connections. No inbound firewall rules required, ever.
AkkuArka and AkkuReka remain central — one vault, one proxy, one audit log across every environment.
No credentials stored at rest between operations. The agent holds nothing inside the isolated zone.
Adding a new isolated environment takes minutes. No lengthy deployment cycles or provisioning.
Works across cloud VPCs, on-premise datacenters, regulated environments, and fully air-gapped networks.
Banks, hospitals, and manufacturers isolate their most sensitive systems deliberately. This is exactly where most PAM tools break down, their architecture assumes the product can always reach the target. When it can't, they offer two bad options.
More servers to install, harden, patch, and monitor. Each holds admin credentials, a high-value target in the network you were trying to protect. Every new zone means weeks of deployment work.
A VPN or inbound firewall rule, exactly what the security team won't approve. The conversation about access governance becomes a debate about network architecture.
Both options increase complexity, credentials, and attack surface inside the environments that need the least of it.
The architecture was never designed for networks that can't be reached from outside.
The central product stays central, and a tiny courier goes into the isolated network.
AkkuArka
One vault. One admin console. One audit log. Never deployed inside the isolated zone — always central.
AkkuReka
Handles session verification, recording, and credential injection entirely from outside the isolated network.
Akku Agent
Lightweight binary. One persistent outbound connection. No inbound rules. No credentials stored at rest between operations.
How it works
The request lands in AkkuReka's approval queue
An admin approves it
AkkuArka prepares the credential; a throwaway database user, a rotated server password, or a temporary SSH key
The instruction travels to the agent through the existing outbound connection
The agent carries out the operation locally; creates the user, installs the key, or rotates the password; using credentials sent from AkkuArka only for the moment of the operation
The session opens through AkkuReka and is recorded in full
When the session ends, the agent drops the user or rotates the credential immediately

What the Akku agent does inside your isolated network.
OS password rotation
Rotates server account passwords on Linux and Windows systems on instruction from AkkuArka. No standing admin credentials on the agent host.
SSH key lifecycle
Installs and revokes SSH keys on Linux and Windows OpenSSH servers. Keys are issued per grant and revoked when the grant ends.
Database user lifecycle
Creates and drops per-session database users on PostgreSQL, MySQL, and MongoDB. Admin credentials are received from AkkuArka only for the moment of the operation and are never stored locally.
User enumeration
Reports available OS and database users to the central system so administrators see an accurate, current list when approving access requests.
For your security team
The agent looks like any other outbound client to your firewall. No inbound rules means no architecture review, no committee approval cycle, no weeks of back-and-forth. The conversation that used to block deployments doesn't happen.
For your IT team
Deploying Akku PAM into a new isolated environment means shipping one binary and registering it as a service. Not standing up multiple servers. Not deploying an appliance. Not submitting firewall change requests.
For your compliance team
One audit log covers every action across every environment; cloud VPCs, on-premise zones, air-gapped networks. No stitching together logs from appliances in different zones. One export. One place.
For your budget
Adding a new environment adds one agent. The cost curve is flat as your infrastructure grows. You don't pay for, patch, or audit a full PAM stack in every zone.
From cloud VPCs to air-gapped environments.
Private cloud VPCs
AWS, Azure, GCP; where direct management network access is prohibited or impractical
On-premise datacenters
With strict inbound firewall policies or air-gap requirements
Regulated industry environments
BFSI, healthcare, defence; where inbound connections to sensitive zones are prohibited by policy or regulation
Multi-tenant environments
Where each customer's environment is isolated from the management network and from each other
Hybrid environments
Some resources reachable directly by AkkuReka, others only via the agent, all managed from one central console
Akku's isolated network model directly addresses requirements across:
Akku PAM is built for IT and security teams who need clear answers about how privileged access works, what the product does, and what it means for your infrastructure and compliance posture.
If you have a question that isn't covered here, please and we will be happy to address your queries.