In an earlier article, we explored the 3 pillars of a Cloud Access Security Broker (CASB), with Identity and Access Management (IAM) being one of these pillars. In this blog, we dive deeper into IAM, and the key concepts on which it is built.
2021 saw the average cost of a data breach rising from US$3.86 million to US$4.24 million on an annual basis, according to the IBM Cost of a Data Breach Report 2021.
Data breaches are increasing. And your Identity and Access Management solution, or IAM, is your first line of defense. IAM secures, measures, monitors, and improves the security of access through a standardized process.
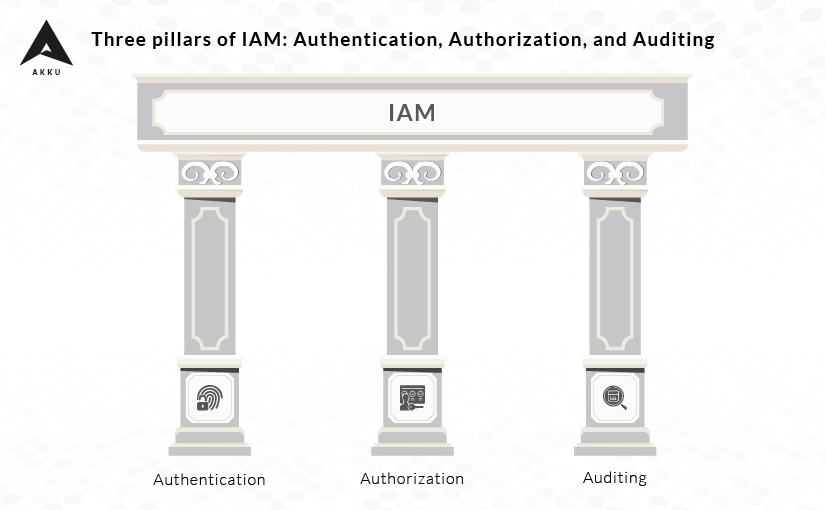
How does an IAM improve security? It offers three pillars of support: Authentication, Authorization, and Auditing.
Authentication
How do you map the correct users to gain access to the correct content, at the correct times?
Authentication takes place whenever a user attempts to access the organization’s network or assets. Verified credentials serve as a passport that allows users to access data, systems, applications, and resources.
With data breaches becoming more common, user authentication is vital to security. Organizations are prioritizing advanced security through sophisticated additional authentication methods. For instance, your IAM would secure your access management with two-factor or multi-factor authentication by pairing a username and password with a key card or OTP token, a fingerprint, or facial recognition. Every user has unique credentials, and IAM authenticates the user data to confirm that the user is a member of the organization.
Using a strong password policy can also improve authentication security. Verifying whether your IAM allows you to configure and customize your password policy is essential in providing a comprehensive authentication process.
Authorization
While authentication verifies the users’ identity, the authorization aspect of IAM is what grants the user access to data based on their identity and defined access rules. While the two are related, they are not interchangeable.
In a sense, authorization is the second step to authentication – think of a night club, where the bouncer allows you entry after checking your ticket stamp (authentication), following which another staffer inside decides if your stamp allows you access to every area of the club or restricts you to select areas (authorization).
In organizations, users are granted authorizations according to their roles. Proper authorization is important to prevent data breaches.
For secure authorization, follow the zero trust principle and provide minimum possible access to each active user and immediately deprovision ex-employees. These two steps ensure that the risk of data breaches caused by improper authorization or disgruntled employees is reduced.
Auditing
Auditing security configurations helps weed out redundancies within the IAM system, such as IAM users, roles, and policies that are not required, and make sure that all users are authorized and authenticated. It also helps secure the system by regularly monitoring who has access to critical enterprise assets.
Audits ensure that compliance requirements are met, incidents are responded to and taken care of within a defined period of time, procedures are streamlined, responsibilities are segregated, transparency and documentation are maintained.
Audits can also help to understand employee or user contributions on a particular app or data sheet. This can also be used in version control. Knowing who last logged on to the document gives usable information in cases where data has been breached.
Chinks in authentication, authorization, or auditing can result in a compromised system. Opt for a trusted IAM solution such as Akku, a major emerging player in the APAC region. Akku offers a plethora of customizable options to improve data security, standards compliance, efficiency, and productivity.