To stick with passwords or to go passwordless is a million-dollar cyber security question. Resetting, remembering, and changing passwords regularly is not only frustrating but puts critical information at risk. But at the same time, have we reached a point where we can realistically remove passwords entirely from our authentication processes?
The drawbacks of passwords
Strong passwords are difficult to remember, and weak passwords are too easy to hack. Additionally, overuse of the same passwords across multiple platforms can result in breaches during credential stuffing attacks.
According to a report from LastPass, weekly time spent managing users’ passwords and login information has increased 25% since 2019. The report also says that 85% of employees agree that their organization should reduce the number of passwords required to be used daily. And according to Verizon data, 81% of data breaches involve weak, default, or stolen passwords.
What is Passwordless Authentication?
Passwordless authentication is user-friendly and secure and brings to the table reduced IT costs by eliminating password-related risks, increased productivity as employees save time remembering or updating passwords, and stronger security. In short, passwordless authentication is both convenient and secure.
Passwordless authentication relies on the same principles as digital certificates, on public and private keys. Think of the public key as the padlock and the private key as the key that unlocks it. With digital certificates, there is only one key for the padlock and only one padlock for the key. For passwordless authentication, a cryptographic key pairs with a private and a public key. A user wishing to create a secure account uses a mobile app to generate a public-private key pair, where the public key is provided to the system, and the private key is accessed from the user’s local device using an authentication factor such as an OTP.
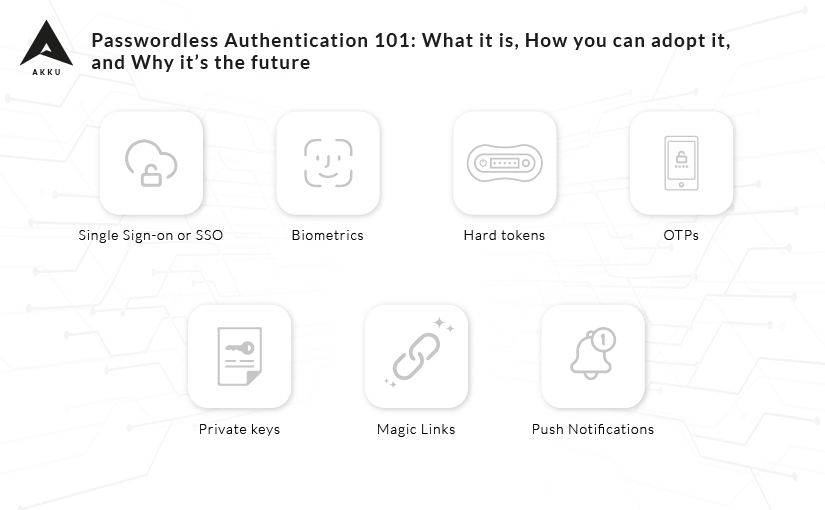
Here are some ways you can go passwordless
- Single Sign-on or SSO
It simplifies managing access and provides employees an easy and secure way to log in. Also, it allows IT to provision or deprovision access as needed. However, while SSO reduces the number of passwords required, it often demands a single password to access all applications. - Biometrics
Fingerprints, face, iris, voice, and other biometric parameters are used as they are considered more challenging to hack than alphanumeric codes. They are also convenient to use, as they cannot be misplaced, stolen or forgotten. - Hard tokens
They allow access to software after verification with a physical device. - OTPs
Users are asked to input the code sent to them via email or SMS. OTPs provide an additional layer to security and are more secure than static passwords. OTPs are often used as a second layer of authentication, but can even replace static passwords. - Private keys
An alphanumeric string is processed through an algorithm, to encrypt or decrypt data. - Magic Links
Users enter their email address in a form, and then an email is sent with a login link. - Push Notifications
Users receive a push notification on their mobile devices through a dedicated authenticator app for identity verification.
Passwordless authentication methods are compatible across most devices and systems. Plus, they’re virtually impervious to phishing and other common cyberattacks.
So, is passwordless authentication the future?
Passwordless methods offer both a more secure and a more convenient way to authenticate users. So the simple answer is, yes, they are the future.
However, considering how ubiquitous passwords are today, they certainly aren’t going to disappear overnight. So until passwordless methods gain in popularity, it’s important to continue to do all you can to ensure strong passwords to secure your applications and data.
Whether you are ready to take the leap to passwordless, or are looking for a way to make your password based authentication more secure, Akku can help you enhance security and productivity across your environment. Talk to us today to see how we can help.